Google-Bericht: Mehr Zero-Day-Schwachstellen, die Unternehmen betreffen
Wie Zero-Day-Exploits die Bedrohungen der Unternehmens-Security verändern
Die wichtigsten Erkenntnisse
- Zero-Day-Schwachstellen beeinträchtigen zunehmend Unternehmen, wobei sowohl die Anzahl als auch der Anteil der betroffenen Technologien im Jahr 2025 Rekordwerte erreichen.
- Die Hälfte der auf Unternehmen ausgerichteten Zero-Day-Angriffe zielte auf Netzwerk- und Security-Software ab, was zeigt, dass sich die Angreifer nun auf kritische Unternehmensinfrastrukturen konzentrieren.
- Betriebssysteme waren die am häufigsten ausgenutzte Produktkategorie und machten 44 % aller Zero-Day-Schwachstellen aus, während Browser weniger als 10 % ausmachten.
- Die Massenausnutzung nimmt zu, d. h., dass nationalstaatlich unterstützte Gegner immer besser darin werden, Exploits schnell zu entwickeln und zu verteilen.
Eine Analyse der Google Threat Intelligence Group (GTIG) von 90 Zero-Day-Schwachstellen, die 2025 tatsächlich ausgenutzt wurden, legt nahe, dass Cyberangriffe sich stärker auf anspruchsvollere Unternehmensziele konzentrieren.
Sowohl die Anzahl (43) als auch der Anteil (48 %) der Schwachstellen, die Unternehmenstechnologien betreffen, erreichten Allzeithöchststände und machten fast 50 % der insgesamt ausgenutzten Zero-Days im Jahr 2025 aus. Unter diesen Schwachstellen zielte etwa die Hälfte (21) speziell auf Netzwerk- und Security-Software ab.
Dem Bericht zufolge machten Betriebssysteme, sowohl Desktop- als auch mobile, im Jahr 2025 die am häufigsten ausgenutzte Produktkategorie und 44 % (39) aller Zero-Day-Schwachstellen aus. Browser hingegen waren 2025 für weniger als 10 % der Zero-Day-Exploits verantwortlich. Allerdings wurden mehrere Browser-Sandbox-Escape-Sequenzen entdeckt, die jeweils speziell darauf ausgelegt waren, Komponenten des zugrunde liegenden Betriebssystems oder der verwendeten Hardware auszunutzen.
Außerdem wurden Schwachstellen in größerem Umfang ausgenutzt. Das deutet darauf hin, dass Gegner, die im Namen von Nationalstaaten arbeiten, zunehmend geschickter darin geworden sind, Exploits zu entwickeln, zu teilen und zu verteilen.
Sich wandelnde Taktiken und Techniken
Insgesamt deutet der CTIG-Bericht darauf hin, dass die Ausnutzung von Unternehmensanwendungen weiterhin einen großen Anteil dieser Angriffe ausmachen wird, da die Bandbreite der eingesetzten Anwendungen die gesamte Angriffsfläche, die Cybersicherheitsteams verteidigen müssen, immer weiter vergrößert, während gleichzeitig Angreifer künstliche Intelligenz (KI) einsetzen, um Schwachstellen schneller zu entdecken und auszunutzen.
Außerdem scheinen sich auch die von Gegnern eingesetzten Taktiken und Techniken weiterzuentwickeln. So weist der Bericht beispielsweise darauf hin, dass eine BRICKSTORM-Malware-Kampagne, die einer Spionagegruppe mit Verbindung zur Volksrepublik China zugeschrieben wird, geistiges Eigentum ins Visier nahm, darunter Quellcode und proprietäre Entwicklungsdokumente. Diese IP könnte dazu verwendet werden, Schwachstellen in der Software zu entdecken, um nachgelagerte Kunden anzugreifen.
Positiv ist jedoch, dass die KI es den Verteidigern ermöglichen sollte, Schwachstellen proaktiver zu entdecken und bei Bedarf Patches zu entwickeln, zu testen und zu verteilen, so der Bericht.
Häufige Angriffsvektoren
Zero-Day-Exploits werden meist primär zur Ausführung von Remote-Code ausgenutzt, gefolgt von einer Rechteausweitung. Command Injection und Techniken zur Deserialisierung, die strukturierte Daten wieder in ein Objekt oder eine Datenstruktur umwandeln, die ein Programm verwenden kann, waren kritische Vektoren im Unternehmen. Bösartige Akteure setzen weiterhin auf Speicherbeschädigungen, die für 35 % der Schwachstellen verantwortlich waren.
Andere häufige Angriffsvektoren umfassten auch die Umgehung von Authentifizierungs- und Autorisierungsmechanismen sowie Exploits von Logik- und Designfehlern, die häufig in Unternehmensgeräten zu finden sind.
Im Allgemeinen rät der GTIG-Bericht den Einsatz von Firewalls, um eine inhärente Segmentierung und Least-Privilege-Zugriffskontrollen zu ermöglichen und so weitere dieser Angriffe zu verhindern. Darüber hinaus sollten Cybersecurity-Teams auch in Tools zur Überwachung investieren, um Sicherheitsverletzungen aufzudecken, die aktuell nahezu unvermeidlich sind, so der Bericht.
Cybersecurity-Teams sollten auch eine Software-Stückliste (SBOM) pflegen, die im Falle eines Angriffs die Identifizierung der möglicherweise betroffenen Software-Bibliotheken erleichtert.
Wie Willie Sutton einmal bemerkte, rauben Kriminelle Banken aus, weil dort das Geld ist. Diese Denkweise gilt im Zeitalter der Informationstechnologie nun auch für IT-Organisationen in Unternehmen.
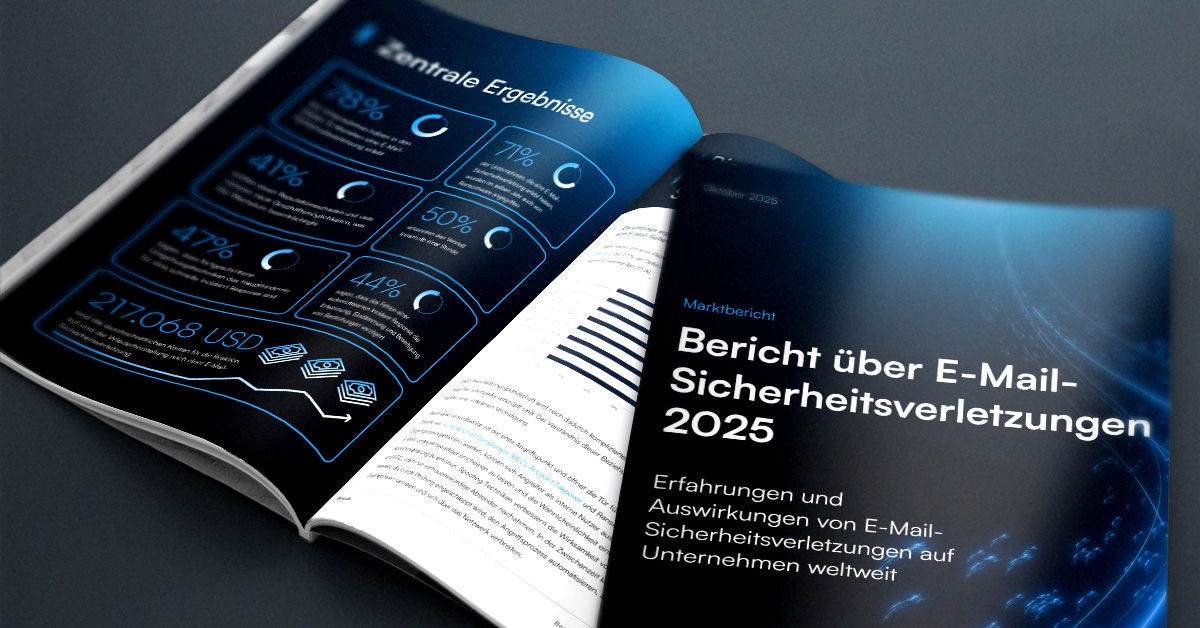
Bericht über E-Mail-Sicherheitsverletzungen 2025
Wichtige Erkenntnisse über die Erfahrungen mit und Auswirkungen von E-Mail-Sicherheitsverletzungen auf Unternehmen weltweit
Abonnieren Sie den Barracuda-Blog.
Melden Sie sich an, um aktuelle Bedrohungsinformationen, Branchenkommentare und mehr zu erhalten.

Der MSP Customer Insight Report 2025
Ein globaler Blick darauf, was Organisationen von ihren Cybersecurity Managed Service Providers benötigen und erwarten.